- Details
![]() Currently I reinstalled my Samsung Galaxy S (with insanity 6.3) and came across "an error occured while downloading your recovery." when trying to flash clockworkmod recovery. With installing a superuser version from the market and reinstalling clockworkmod my problem seems to be solved. There seems to be a bug in the superuser app I was using previously.
Currently I reinstalled my Samsung Galaxy S (with insanity 6.3) and came across "an error occured while downloading your recovery." when trying to flash clockworkmod recovery. With installing a superuser version from the market and reinstalling clockworkmod my problem seems to be solved. There seems to be a bug in the superuser app I was using previously.
- Details
![]() I recently installed a usb-harddisk on my server and mounted it on a guest with virt-manager. The performance was very bad, i had 50Kbyte when testing with hdparm.
I recently installed a usb-harddisk on my server and mounted it on a guest with virt-manager. The performance was very bad, i had 50Kbyte when testing with hdparm.
I remounted it in virt-manager as IDE drive instead of USB-Drive and voila i had full performance again. It seems that the USB-drive mounting is a bit bugged.
- Details
![]() I am using KVM for a while now and reinstalled my XEN-Server. I have to mention it's not the same hardware. XEN was on a 2 year old Server with 4G memory and Debian Lenny32, KVM is on a 6 months old 8G memory Server with Debian Squeeze. So i have a bit better hardware and a 64bit System on KVM.
I am using KVM for a while now and reinstalled my XEN-Server. I have to mention it's not the same hardware. XEN was on a 2 year old Server with 4G memory and Debian Lenny32, KVM is on a 6 months old 8G memory Server with Debian Squeeze. So i have a bit better hardware and a 64bit System on KVM.
I like that KVM is out-of-the-box working with virsh/virt-manager the performance improvement is enormous, especially with 64MB-RAM systems like I use for my wiki. I use LVM for the guest-disks (I did it even for the XEN-guests) and compared to use files it's even a huge performance improvement.
The only thing that's easier in XEN is that you can mount the guest-partitions and can access them directly in KVM you need to use kpartx (not hard but one step more) to achieve this.
I started to move to KVM because it seems as XEN development slowed down and there is much more development activity and support for KVM. I think that was a good decision.
- Details

![]()
I recently needed to install a Oracle 11g Database on Debian, and wrote down the notes here. Please send me a message
if i missed a step or something is easier to achieve than I did.
install mandatory packages
some packages are probably not necessary, I put them together from old notes from me and several weblinks if you know which are not necessary send me a list and i will correct it
apt-get install binutils autoconf automake bzip2 gcc less libc6-dev make libstdc++5 unzip zlibc build-essentials libaio1
!!!doxygen reported as not needed by Tobia, tx for this! Also watch his comment if you use OpenVZ!
x-terminal
I chose fluxbox but you can also take anything else like xterm, gnome, kde….
apt-get install fluxbox
prepare user and groups
groupadd oinstall
groupadd dba
useradd oracle -m -d /home/oracle -g oinstall -G dba -s /bin/bash
passwd oracle
check environment
there are several kernel parametersw that have to be changed to succesfully install the database, here is a script that helps you to determine them
echo "sem: ";echo "min 250 32000 100 128"; echo "is " `cat /proc/sys/kernel/sem`; echo; \
echo "shmall: ";echo "min 2097152"; echo "is " `cat /proc/sys/kernel/shmall`; echo; \
echo "shmmax - should be able to hold the SGA - max 4G-1byte: ";echo "is " `cat /proc/sys/kernel/shmmax`; echo; \
echo "shmmni: ";echo "min 4096"; echo "is " `cat /proc/sys/kernel/shmmni`; echo; \
echo "file-max: ";echo "min 6815744"; echo "is " `cat /proc/sys/fs/file-max`; echo; \
echo "ip_local_port_range: ";echo "min/max 9000 65500"; echo "is " `cat /proc/sys/net/ipv4/ip_local_port_range`; echo; \
echo "rmem_default: ";echo "min 262144"; echo "is " `cat /proc/sys/net/core/rmem_default`; echo; \
echo "rmem_max: ";echo "min 4194304"; echo "is " `cat /proc/sys/net/core/rmem_max`; echo; \
echo "wmem_default: ";echo "min 262144"; echo "is " `cat /proc/sys/net/core/wmem_default`; echo; \
echo "wmem_max: ";echo "min 1048576"; echo "is " `cat /proc/sys/net/core/wmem_max`; echo; \
echo "aio-max-nr: ";echo "max 1048576"; echo "is " `cat /proc/sys/fs/aio-max-nr`; echo;
change necessary parameters
you have just to change the parameters that don't fit, but feel free to set them all to the minimum with this script
echo "kernel.sem = 250 32000 100 128" >> /etc/sysctl.conf
echo "kernel.shmall = 2097152" >> /etc/sysctl.conf
# !!!! needs to fit YOUR SGA (=main memory for database, be sure to have enough ram for PGA etc.)!!!!
echo "kernel.shmmax = 1200000000" >> /etc/sysctl.conf
#echo "kernel.shmmni = 4096" >> /etc/sysctl.conf
echo "fs.file-max = 6815744" >> /etc/sysctl.conf
#echo "net.ipv4.ip_local_port_range = 1024 65000" >> /etc/sysctl.conf
echo "net.core.rmem_default = 262144" >> /etc/sysctl.conf
echo "net.core.rmem_default = 262144" >> /etc/sysctl.conf
echo "net.core.rmem_max = 4194304" >> /etc/sysctl.conf
echo "net.core.wmem_default = 262144" >> /etc/sysctl.conf
echo "net.core.wmem_max = 1048576" >> /etc/sysctl.conf
echo "fs.aio-max-nr = 1048576" >> /etc/sysctl.conf
change some limits
also some limits have to be set
echo "oracle soft nproc 2047" >> /etc/security/limits.conf
echo "oracle hard nproc 16384" >> /etc/security/limits.conf
echo "oracle soft nofile 1024" >> /etc/security/limits.conf
echo "oracle hard nofile 65536" >> /etc/security/limits.conf
create directories
I prefer to separate software, database files and recovery files so i put them in /u01 /u02 /u03
mkdir -p /u01/app/oracle
mkdir -p /u02/oradata
mkdir -p /u03/flash_recovery_area
chown -R oracle:oinstall /u01 /u02 /u03
chmod -R 775 /u01 /u02 /u03
NOTE: seems they just say “recovery_area” or even “fast_recovery_area” now to the “flash_recovery_area”
additional steps
These steps prevent errors when the installer links some libraries
ln -s /usr/bin/awk /bin/awk
ln -s /usr/bin/basename /bin/basename
finish preparations
reboot
== call the installer But before calling the installer check with above script if the kernel parameters are fine now
su oracle
/pathtoinstallfileshere/database/runInstaller -ignoreSysPrereqs
installer
The installer should guide you through each step in simple and advanced mode. When the requirements are checked you can savely bypass the warnings, because not everything can be checked on an unsupported ;-) environment.
!!!I really want to keep this up-to-date so please send me a note if i missed something or something is easier to handle than i did it!!!
Errors that can happen and how to bypass them
Added at 30.12.2010 including some more install packages some of the errors below did not happen when i wrote this article, it seems some new library versions etc. changed recentlyjava exception when calling the installer
happened at my side because I installed it over vnc This should help:
xhost localhost
Error in invoking target 'install' of makefile ins_ctx.mk
seems to be a problem with a newer? glibc version in the make.log file you should find something like
warning: libstdc++.so.5, needed by /u01/app/oracle/product/11.2.0/dbhome_1/ctx/lib//libsc_fa.so, not found
simply install libstdc++5 apt-get install libstdc++5
- Details
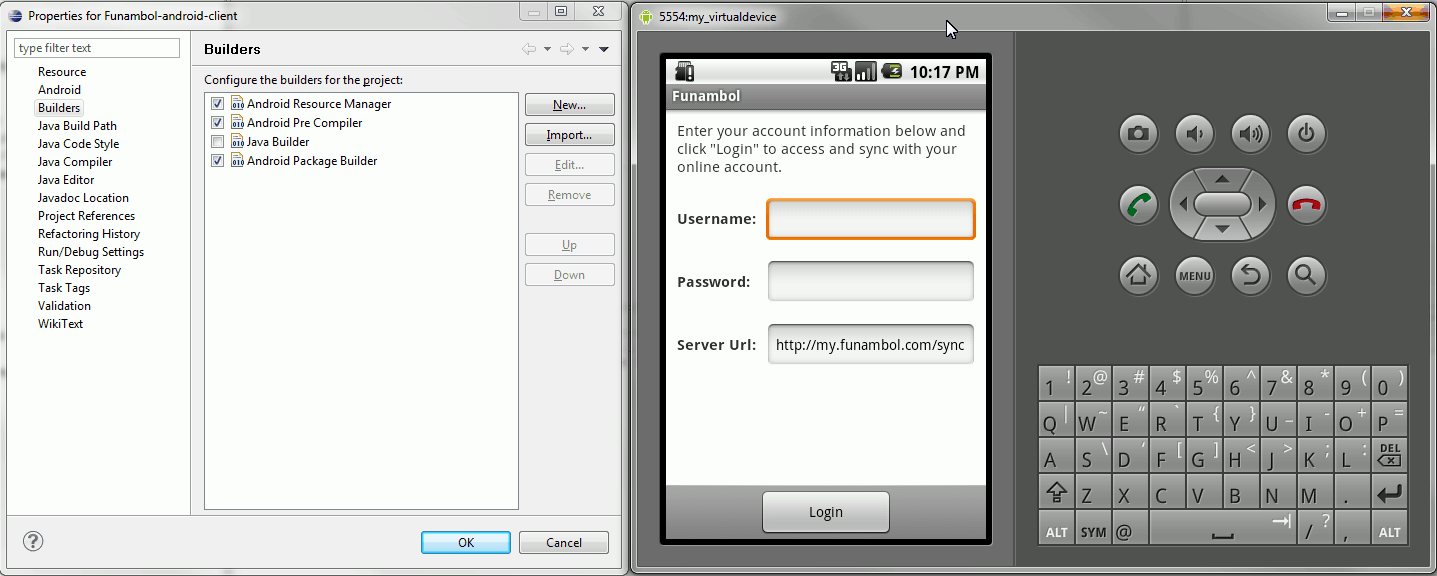
That's the message you get in Eclipse if you try to build the Funambol Android Sync Client.
Reason is that you have checked two Builders that try to generate the same class.
You just have to uncheck the Java-Builder from Project->Properties->Builders.
Then the application even works fine in the Emulator.
- Details
Some time ago (after noticing my stuff was not working anymore  ), I wrote a Utility Class for the Amazon Product API. I now published it as part of my new Amazon Tools project, that can be downloaded as complete class with examples here. It's licensed under Simplified BSD License.
), I wrote a Utility Class for the Amazon Product API. I now published it as part of my new Amazon Tools project, that can be downloaded as complete class with examples here. It's licensed under Simplified BSD License.
/**
* signs the request Url for the Amazon API
* @param str pUrl unsigned Url
* @param str pSecretAccessKey it's a hash to sign the Url,
* you get that from the Amazon-Partner network
* together with your AccessKey
* @return signed Url
*/
function &signRequestUrl($pUrl,$pSecretAmazonHash){
// retrieve Parameter from urls
$arrUrlParts = parse_url($pUrl);
$vParams = $arrUrlParts['query'];
// parameters are separated by & so we put them in
// another array, in there are values like "aa=bb" "xx=yy"
$arrParams = explode('&',$vParams);
// loop and put pair/values in array
foreach($arrParams as $vPair){
// easy separating of the name/val by using explode
$arrPair = explode('=',$vPair);
$arrParamsSort[$arrPair[0]] = $arrPair[1];
}
// Timestamp needed if there is none present
$arrTemp = array_change_key_case($arrParamsSort,CASE_UPPER);
// format from amazon-docs
if (empty($arrTemp['TIMESTAMP'])){
$arrParamsSort['Timestamp'] = gmdate('Y-m-d\TH:i:s\Z');
}
// sort the array, needed to make the Url canonical
ksort($arrParamsSort);
// canonical means that the parameters are sorted
// so it's easier to check if urls are different
$vCanonicalString = '';
foreach ($arrParamsSort as $vKey => $vVal){
// rawurlencode => 5.3 should be RFC 3986 compliant
// for php versions below this should do the job
$vNewVal = str_replace('%7E','~', $vVal);
$vCanonicalString = $vCanonicalString.$vKey.'='.rawurlencode($vNewVal).'&';
}
// remove last &
$vCanonicalString = rtrim($vCanonicalString,'&');
// from he amazon docs
$vSignString = "GET\n".strtolower($arrUrlParts['host']).
"\n".$arrUrlParts['path']."\n".$vCanonicalString;
// generate the hash from the request
$vSignature = hash_hmac('sha256',$vSignString,$pSecretAmazonHash,true);
// and base64 encode it
$vSignature = rawurlencode(base64_encode($vSignature));
// rebuild the url with the signature
$vRet = $arrUrlParts['scheme']."://".$arrUrlParts['host'].
$arrUrlParts['path']."?".$vCanonicalString."&Signature=".$vSignature;
return $vRet;
}
- Details
I was looking for a solution to use multiple desktops in Windows7 like its possible on Linux since.... ever?
To use multiple desktops is very convenient if you develop software, a lot of application are often just used once ore twice a day but you have to tab through them very often. There seems to be no solution from Microsoft, and i could not really find any other good solution, until i ran over Virtual Dimension. The last update was in 2005. I was very skeptical because the software was not maintained for over five years. But... this is why i write this article its GREAT STUFF!. Why?
- it installs pretty fast and is pretty small (~400k)
- very easy to configure, intuitive handling
- possible to use drag and drop of the applications (you can move your applications between the desktops
I dont know how it can be possible that somebody writes software that works for five years on different OS versions, but its incredible.
I hope Francois Ferrand will continue to work on this project.
- Details
so that the jar-file just could not be found.
1 |
java.security.AccessControlException: |
- Details
![]() If you get that error when invoking the Oracle-Forms Layout-Editor and you are sure the naming of the bean and also the FORMSxx_BUILDER_CLASSPATH variable is set correctly, then you should check with which java-version your bean is compiled. To display it correctly in version 10.x you need JDK 1.4.2_06 or lower. I don't know which version you need for version 11, please comment if you have any infos about that.
If you get that error when invoking the Oracle-Forms Layout-Editor and you are sure the naming of the bean and also the FORMSxx_BUILDER_CLASSPATH variable is set correctly, then you should check with which java-version your bean is compiled. To display it correctly in version 10.x you need JDK 1.4.2_06 or lower. I don't know which version you need for version 11, please comment if you have any infos about that.
- Details
![]() If you programmatically modify a window by using SET_WINDOW_PROPERTY a WHEN-WINDOW-RESIZED event should be triggered. If in the meantime a message is dispatched by a bean (WHEN-CUSTOM-ITEM-EVENT) the WWRSZ is NOT processed. It seems to be a matter of timeing how long the message to the server takes because it does not always occur (of course same code.... nothing changed...).
If you programmatically modify a window by using SET_WINDOW_PROPERTY a WHEN-WINDOW-RESIZED event should be triggered. If in the meantime a message is dispatched by a bean (WHEN-CUSTOM-ITEM-EVENT) the WWRSZ is NOT processed. It seems to be a matter of timeing how long the message to the server takes because it does not always occur (of course same code.... nothing changed...).
Hopefully i can reproduce it on a minimal form for the ORACLE-support.
- Details
 If you are using your subversion server with ssh you normally use something like
If you are using your subversion server with ssh you normally use something like
1 |
svn co svn+ssh://
|
for checkout. If your ssh port is not default 22 you have to change a bit in the subversion configuration.
The subversion config file is normally located in the users application-data directory in ...\Subversion and is named config.
In the tunnels you have to add a ssh-client (i used TortoisePlink.exe because i already had TortoiseSVN installed), and configure that the ssh protocol uses a different port by default.
1 |
ssh = C:\\Program Files\\TortoiseSVN\\bin\\TortoisePlink.exe -P 2211
|
1 |
myssh = C:\\Program Files\\TortoiseSVN\\bin\\TortoisePlink.exe -P 2211
|
1 |
svn co svn+myssh://
|
I don't know if it is a bug, but you have to set in TortoiseSVN->Settings->Network->SSH client TortoisePlink again
1 |
"C:\Program Files\TortoiseSVN\bin\TortoisePlink.exe" -P 2211
|
This was an example for windows, if you want to use it on linux/unix you dont need TortoisePlink you can simply use the ssh binary, you also have to convert the backslashes to slashes.
- Details
![]() If you want to install Oracle Devleoper 10g on Vista or Windows 7 you need to follow the note 559067.1 from Oracle. The most important thing is that you need to install Patch 7047034 before you start using the Developer, else you get some nasty errors when opening or compiling forms.
If you want to install Oracle Devleoper 10g on Vista or Windows 7 you need to follow the note 559067.1 from Oracle. The most important thing is that you need to install Patch 7047034 before you start using the Developer, else you get some nasty errors when opening or compiling forms.
- Securing the RBASH?
- sending bacula status mails with smtp authentication
- svnserve with slikSVN
- limit user rights - Jail Shell RBASH (Debian)
- limit user rights - Jail Shell RSSH (Debian)
- limit user rights - Jail Shell SFTP (Debian)
- limit user rights - Jail Shell SSH (Debian)
- Bacula "Network error with FD during Backup"
- port 9240 already in use
- XPlanner+ Permissions for security Manager
- XPlanner Plus
- Cannot configure CacheManager
- Tomcat on Debian
- Oracle Developer Patch 10.1.2.3
- Oracle Reports font subsetting
- Adding Fonts on Unix for Oracle Reports PDF
- Harddisk recovery tools free and not so free
- REP-1352 Font Issue
- Oracle Reports with barcode
- Enterprise-Manager + RMAN No RMAN found, Message file not found
- ORA-1017: invalid username/password when creating database link
- resolv.conf overwritten empty after reboot
- AmazonBestseller which products are cheap?
- 4gb seg fixup errors after upgrading from etch to lenny
- Oracle Bug ORA-07445: exception encountered
- C compiler cannot create executables.
- Oracle Java File permissions
- EM Manager "Compute dynamic property takes too long"
- where to download com_migrator
- PL/SQL Email-Validation
- Power Consumption of Dell Server
- Enterprise Manager and ORA-00018
- Io exception: The Network Adapter could ...
- Centos = Redhat Enterprise Linux
- Enterprise Manager notification not working
- the magic Oracle WITH-clause
- Error in invoking target - Oracle on Debian
- Oracle Installation on Debian for dummys II
- Oracle Installation on Debian for dummys I
- Oracle-Reports Asynchronous calls with SRW-API
- on-commit not working on materialized views
- using Materialized View
- How to determine the character-set in Oracle
- how to compile invalid sys-objects
- ORA-06553: PLS-320: the declaration of the type...
- Access Control with Context/Fine-Grained Access Control
- MDA Vario/Qtek 9100 Ersatzstift/Replacement Stylus
- Versioning of a table in Oracle
- datapump fails with ora-06502
- Where to find Opatch
- How to create a SPFILE from a PFILE
- How to use UTF8 in PDFs created by Oracle-Reports
- Oracle Failsafe and SPFILE
- phone-number check in constraint
- webutil wuc-024 (WUC-24)
- Failsafe ORA-00942 "View or Table does not exist" workaround
- direct access to the database without TNSNAME.ORA
- Failsafe ORA-00942 "View or Table does not exist"
- Connection to host failed. Bad SQL_SCRIPT at - line 227.
- Is Oracle Failsafe just for Databases?
- Do you know Oracle Failsafe???
- REP-56055: Exceed max connections allowed
- Troubles with OracleDataSource
- Enterprise Manager clone Database results in "insufficient disk space"
- How to distribute Oracle Reports Part II
- How to distribute Oracle Reports Part I
- No valid GPS-Signal on Acer N35
- How to use a terminal-file in webforms
- ORA-00257 ORA-16020 Archiver Stuck
- ORA-39002 ORA-39070 ORA-39087 with Datapump
- Installation Forms and Reports Service failed
- Simple Machine Forum
- Don't use timers in webforms - WHY NOT?
- The difference between PJC and Java Beans in Forms
- Forms and Reports Services Standalone
- ORA-00932: inconsistent datatypes
- Compare Database Performance
- Scott and Tiger
- Surprise Surprise Oracle Developer Suite 10gR2
- Working with Oracle Express Edition
- Oracle Express - an Oracle-Database that's for free